FIREMON SOLUTIONS
Zero Trust Network Access
Govern security policy across your zero trust network access (ZTNA) enforcement points with automated policy management and real-time visibility from FireMon.

Govern security policy across your zero trust network access (ZTNA) enforcement points with automated policy management and real-time visibility from FireMon.
Zero trust offers many long-term advantages to organizations looking to protect sensitive data, defend their users and customers, and harden their defenses against unauthorized access. But ZTNA is only one enforcement layer within a broader Zero Trust architecture, and most organizations deploy ZTNA alongside firewalls, cloud security groups, SD-WAN, and SASE platforms.
The result? Policy intent fragments across vendor consoles. Rules drift. Compliance gaps emerge. Security teams lose visibility into what’s actually enforced versus what was intended.
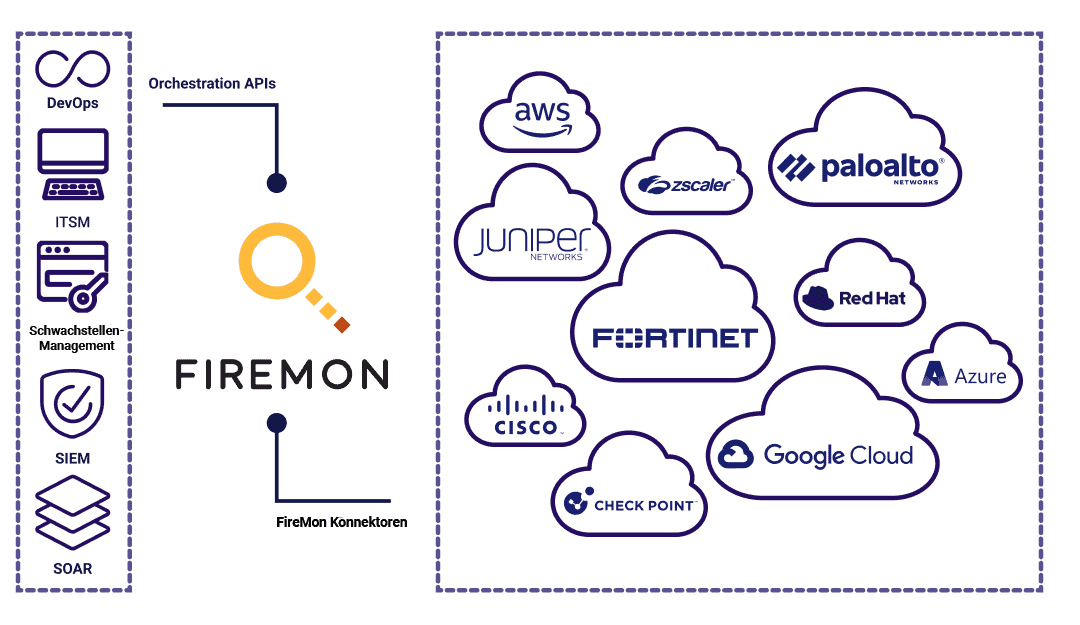
FireMon operates above the enforcement layer, governing policy intent across every ZTNA platform, firewall, and cloud control in your environment. Instead of replacing your security stack, FireMon ensures that your Zero Trust policies are consistently designed, deployed, and maintained across all enforcement points.
ZTNA platforms are enforcement points. They broker access, validate identity, and enforce per-session controls. FireMon is not a ZTNA platform. FireMon is the cross-platform policy governance layer that ensures consistent, compliant, auditable security policy across every enforcement point in your environment—including ZTNA, next-gen firewalls, cloud-native controls, and SASE.
ZTNA Platforms
FireMon
Core Function
Broker and enforce access per session
Govern and manage policy across enforcement points
Scope
Single-vendor access control
Cross-platform policy visibility and governance
Identity & MFA
Validate identity, enforce MFA
Assess policy posture across identity-aware controls
Policy Management
Enforce policies within its own console
Normalize, automate, and audit policy across all vendors
Compliance
Enforce session-level controls
Continuous compliance monitoring across the full stack
Value to Security Teams
Secure access to applications
Eliminate policy drift, reduce risk, maintain auditability
Zero trust isn’t simply a framework or a set of technologies – it’s a mindset. There’s no switch that flips to turn on zero trust access. Organizations have to carefully migrate systems to a zero trust architecture while maintaining the operability of existing infrastructure.
FireMon provides the essential governance layer for organizations transitioning from a perimeter-based network security model to a zero trust security architecture.
FireMon Cyber Asset Management gives your organization a comprehensive view of your network, including everything from physical, cloud-based, virtual, and software-defined network infrastructure and endpoints to operational technology, application access, and the Internet of Things (OT/IoT).
These insights into network traffic data and the current state of enterprise assets are foundational to governing Zero Trust policy at scale. Understanding device posture and asset context across all connected endpoints enables security teams to define and enforce least-privilege access policies across every enforcement point, not just within a single ZTNA console.
FireMon Policy Manager provides a unified view that normalizes policy content across environments containing multiple firewall vendors, cloud security groups, SD-WAN and SASE offerings.
Where ZTNA platforms enforce access at the session level, FireMon governs the policy intent behind those decisions, across policy engine, policy administrator, and policy enforcement point components. This gives teams consistent control over every application and workload, regardless of which vendor is handling enforcement.
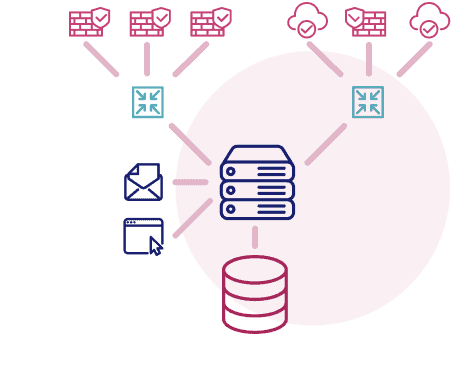
This workflow is often facilitated via API integration into an IT Service Management (ITSM) process such as ServiceNow. As the number of security controls increases within a micro-segmented network, FireMon Policy Manager pushes security policy into all policy enforcement points.
The capability to automate policy governance, from design to decommissioning, frees up security teams for more intensive, mission-critical tasks while reducing policy drift, accelerating provisioning, and ensuring consistent enforcement across the entire security stack.
Transitioning from a traditional perimeter-based security architecture to zero trust often leaves organizations uncertain about where to begin.
FireMon delivers the scalability, flexibility, and real-time visibility to govern Zero Trust policy across your entire enforcement landscape, driven by robust APIs and airtight integrations.
FireMon is one of the best ZTNA solutions, delivering the necessary scalability, flexibility, and real time visibility to support zero trust — driven by robust APIs and airtight integrations.
ZTNA (Zero Trust Network Access) is a security solution that enforces strict identity verification for every user or device attempting to access resources on a network, regardless of their location. Unlike traditional VPNs, ZTNA solutions grant access only to specific applications, reducing the attack surface and enhancing security in dynamic, hybrid environments.
Zero Trust Network Access (ZTNA) works by enforcing strict access control measures, requiring authentication and authorization before users or devices can connect to specific resources. Instead of granting broad access, ZTNA solutions grant access only to authorized applications or data based on identity, device, and security posture, ensuring that each request is verified before access is allowed.
ZTNA (Zero Trust Network Access) grants users access only to authorized applications rather than the entire corporate network. VPNs (virtual private networks) provide broad network-level connectivity once authenticated, which increases lateral movement risk. ZTNA enforces granular, per-application access control and continuously validates user identity and device posture throughout each session.
Identity verification serves as the foundation of every ZTNA solution. The system authenticates each user and device through multi-factor authentication, contextual signals, and real-time security posture checks before granting access to any resource, ensuring that no entity receives implicit trust.
ZTNA solutions provide consistent access management across on-premises data centers, public clouds, and hybrid environments. Organizations apply a single set of security policies regardless of where applications are hosted, ensuring that remote and on-site users receive secure, verified connectivity to every workload.
FireMon helps organizations implement ZTNA by providing automated policy management, real-time network visibility, and continuous compliance monitoring across multi-vendor environments. FireMon bridges existing perimeter-based infrastructure and zero trust architecture so teams can adopt ZTNA without replacing their current security stack.