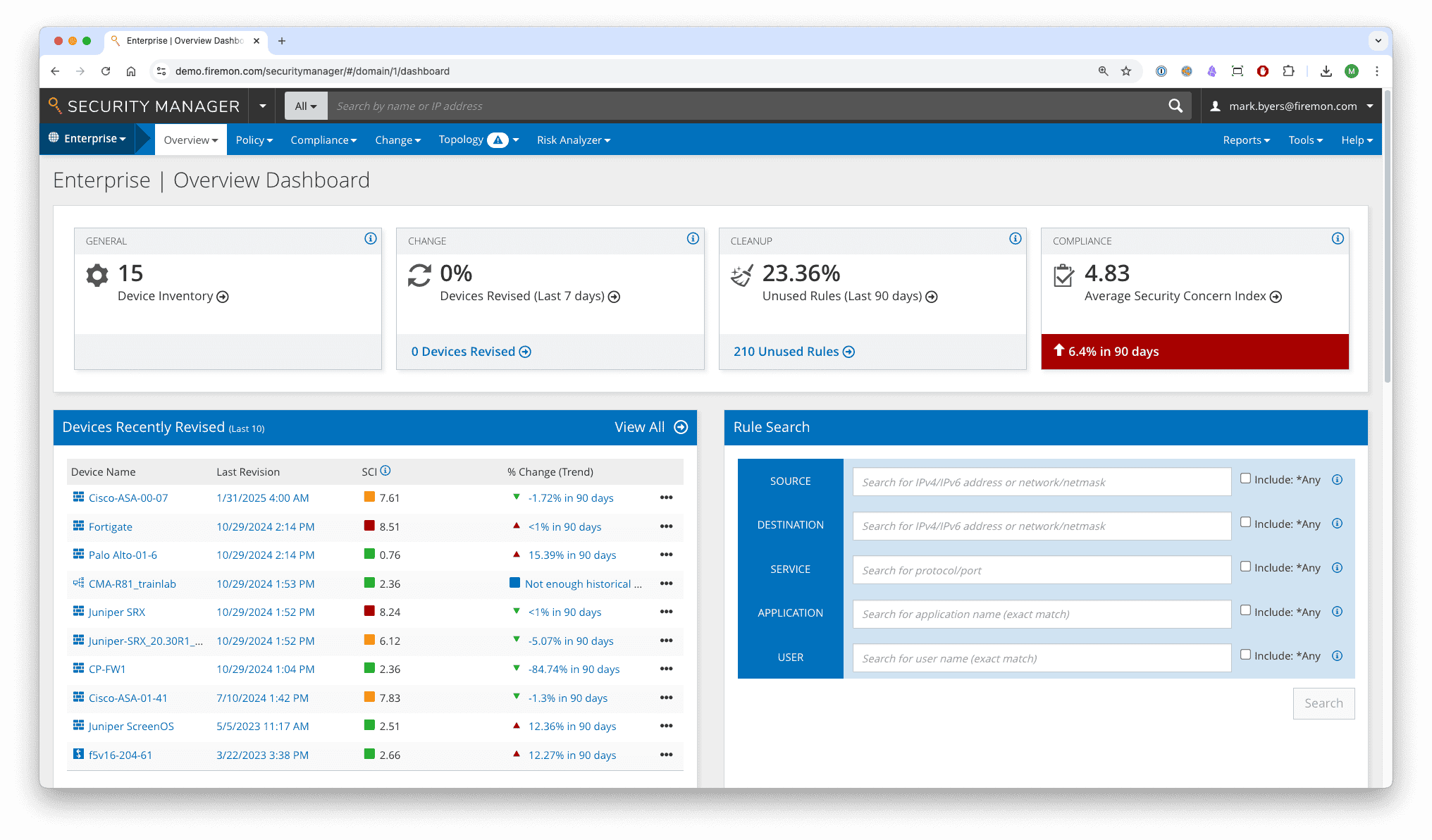
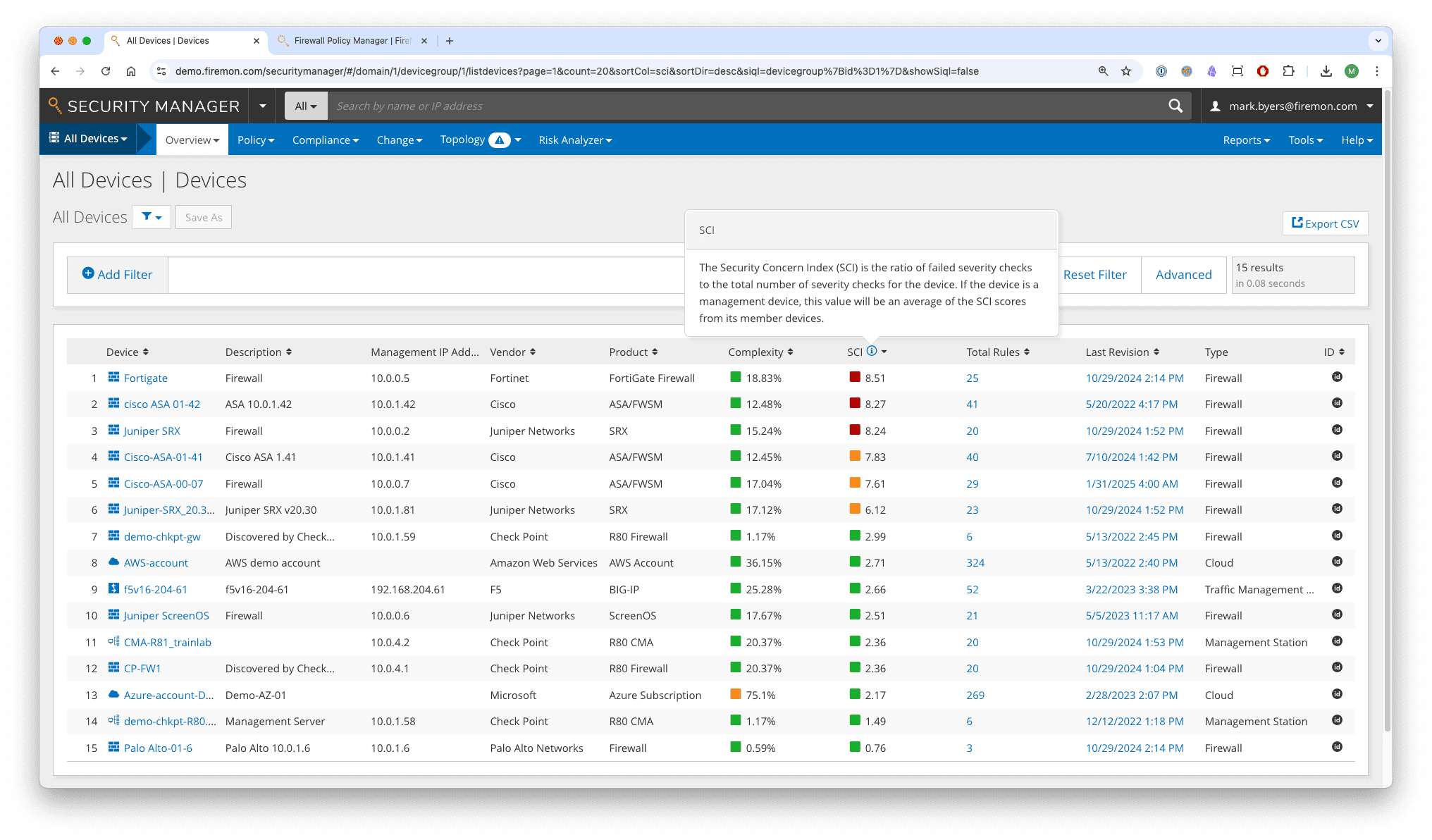
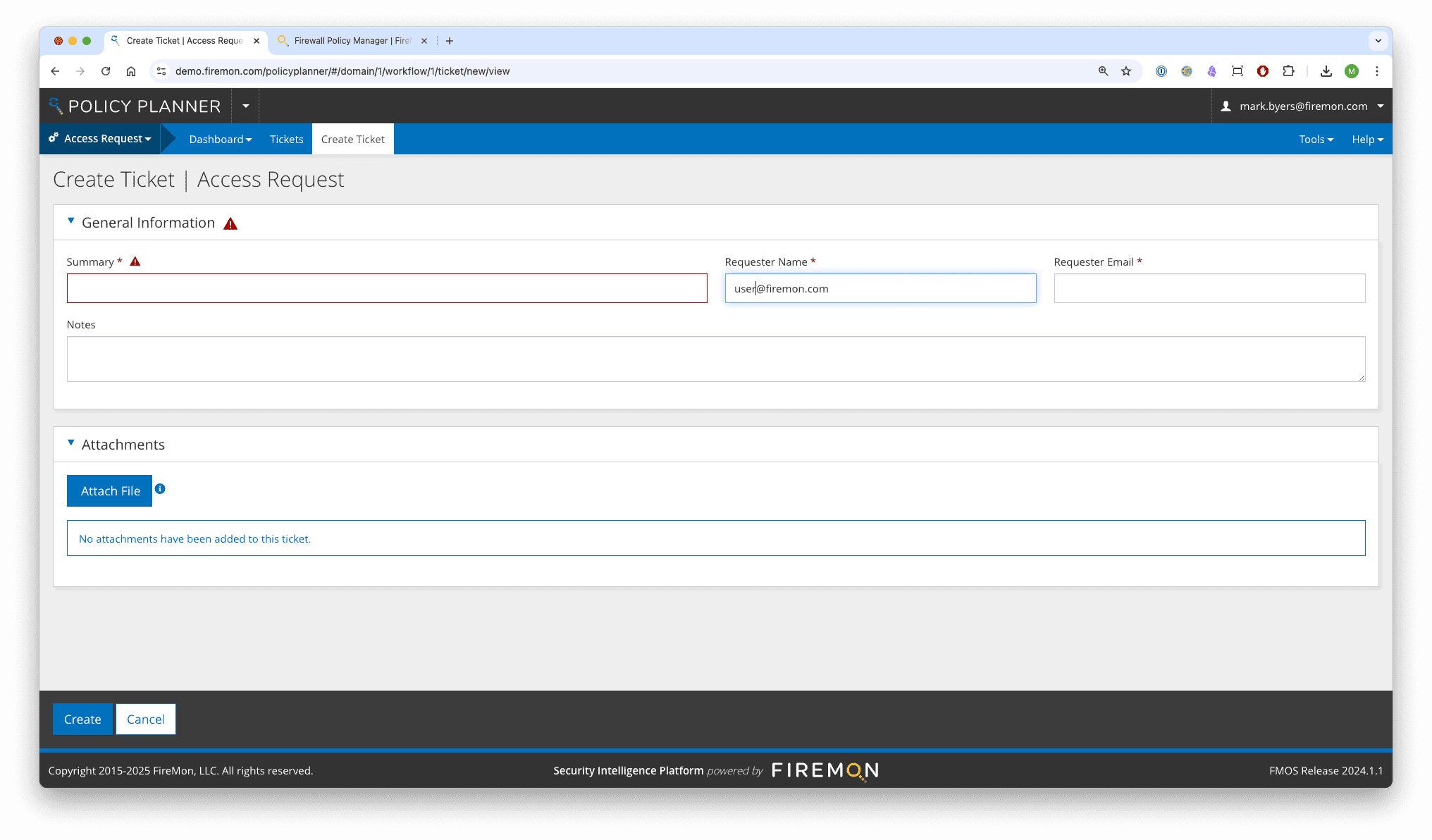
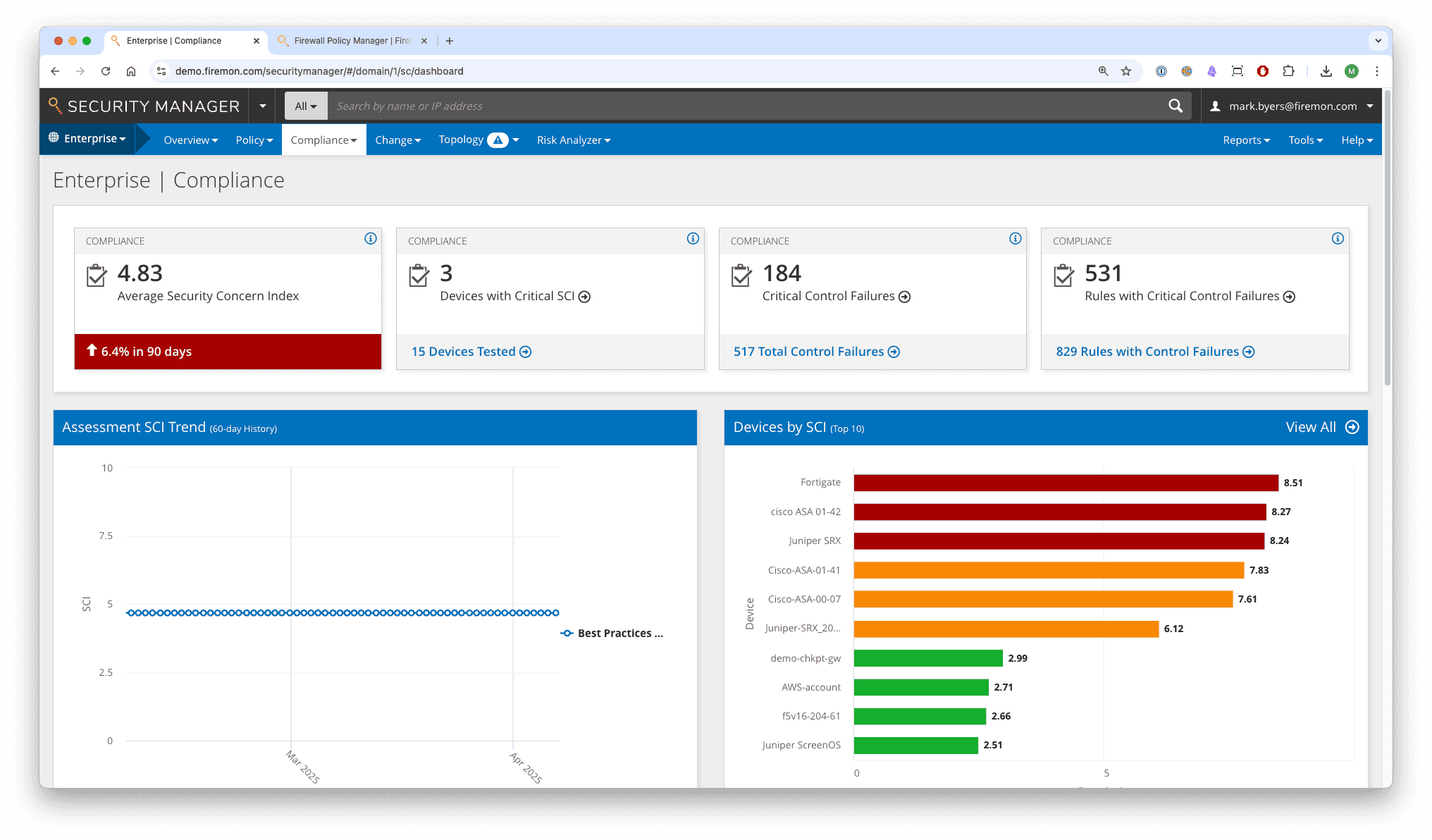
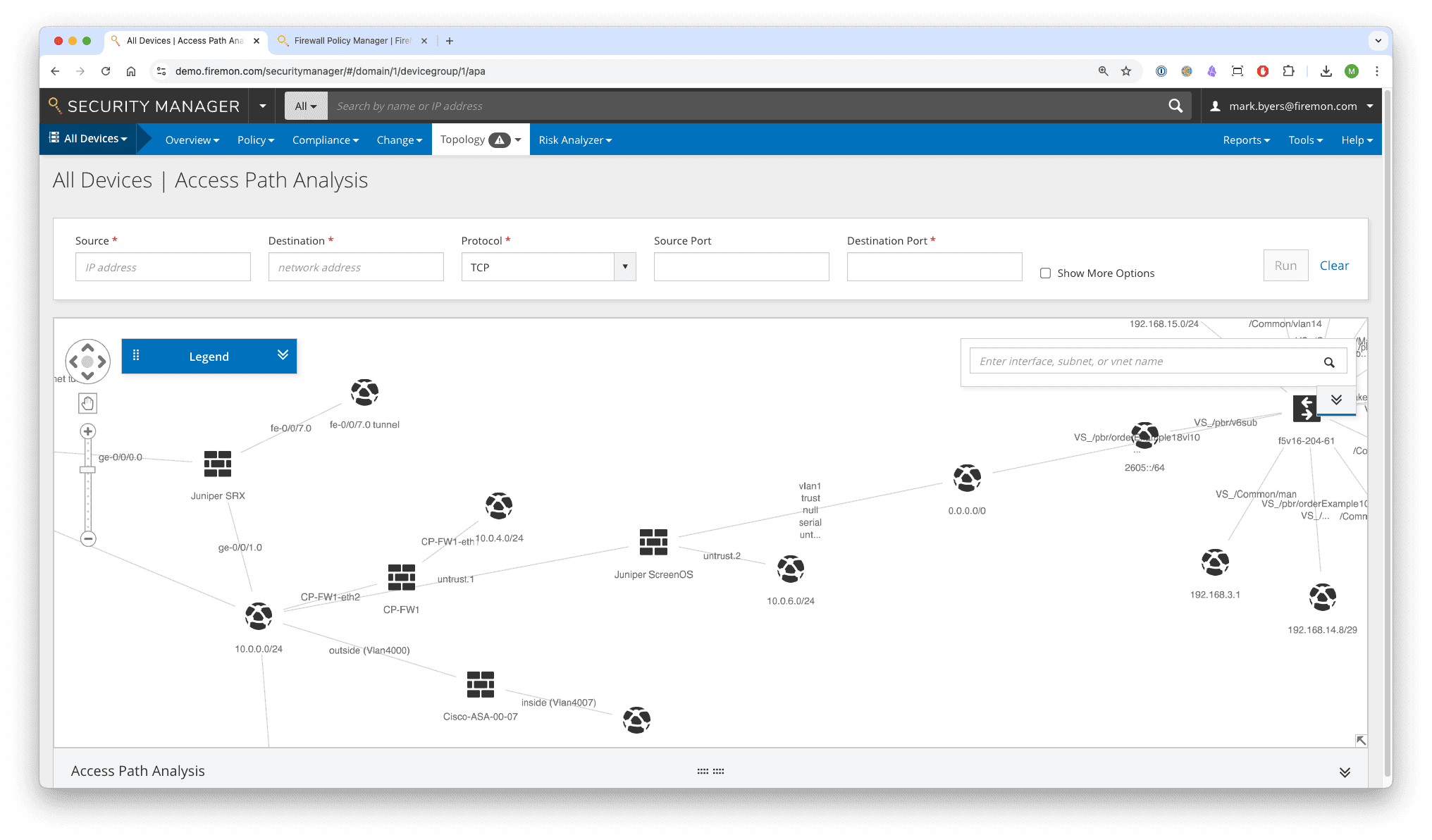
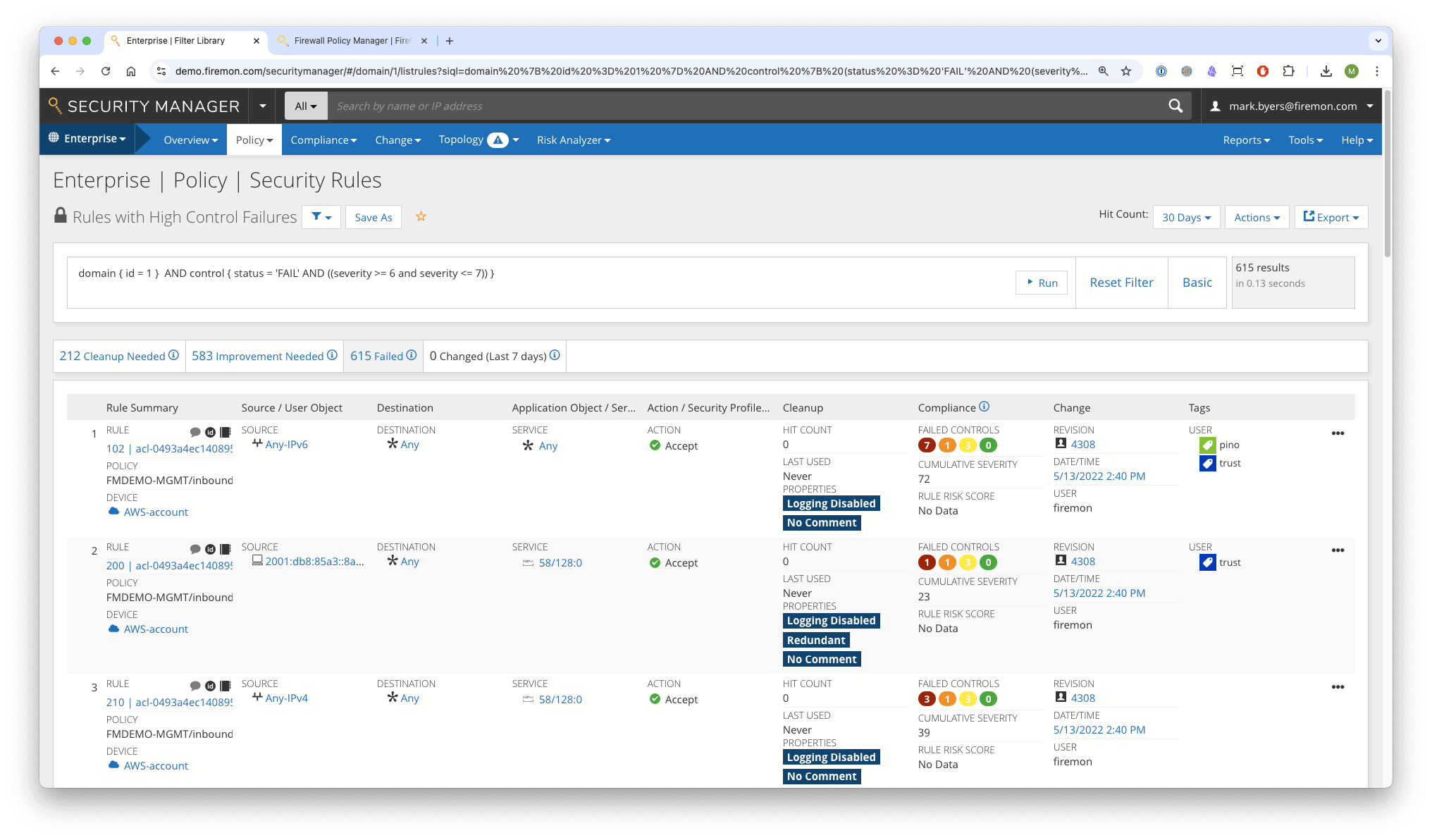
FireMon Policy Manager delivers unified network security policy management for firewalls and cloud security controls across hybrid and multi-cloud environments. The platform provides real-time visibility, proactive risk analysis, and automated policy workflows that validate changes before deployment.
FireMon supports more than 120 firewall, SDN, and cloud platforms, enabling security teams to eliminate misconfigurations, maintain continuous compliance, and accelerate rule changes. It centralizes on-premises and cloud network security policies into a single, scalable system that provides consistent enforcement and audit-ready reporting.