FIREMON PRODUCTS
Asset Manager
Formerly Lumeta
Unmatched real-time cybersecurity asset management that enables network and security
teams to discover the darkest corners of their often-obscure infrastructure.
Formerly Lumeta
Unmatched real-time cybersecurity asset management that enables network and security
teams to discover the darkest corners of their often-obscure infrastructure.
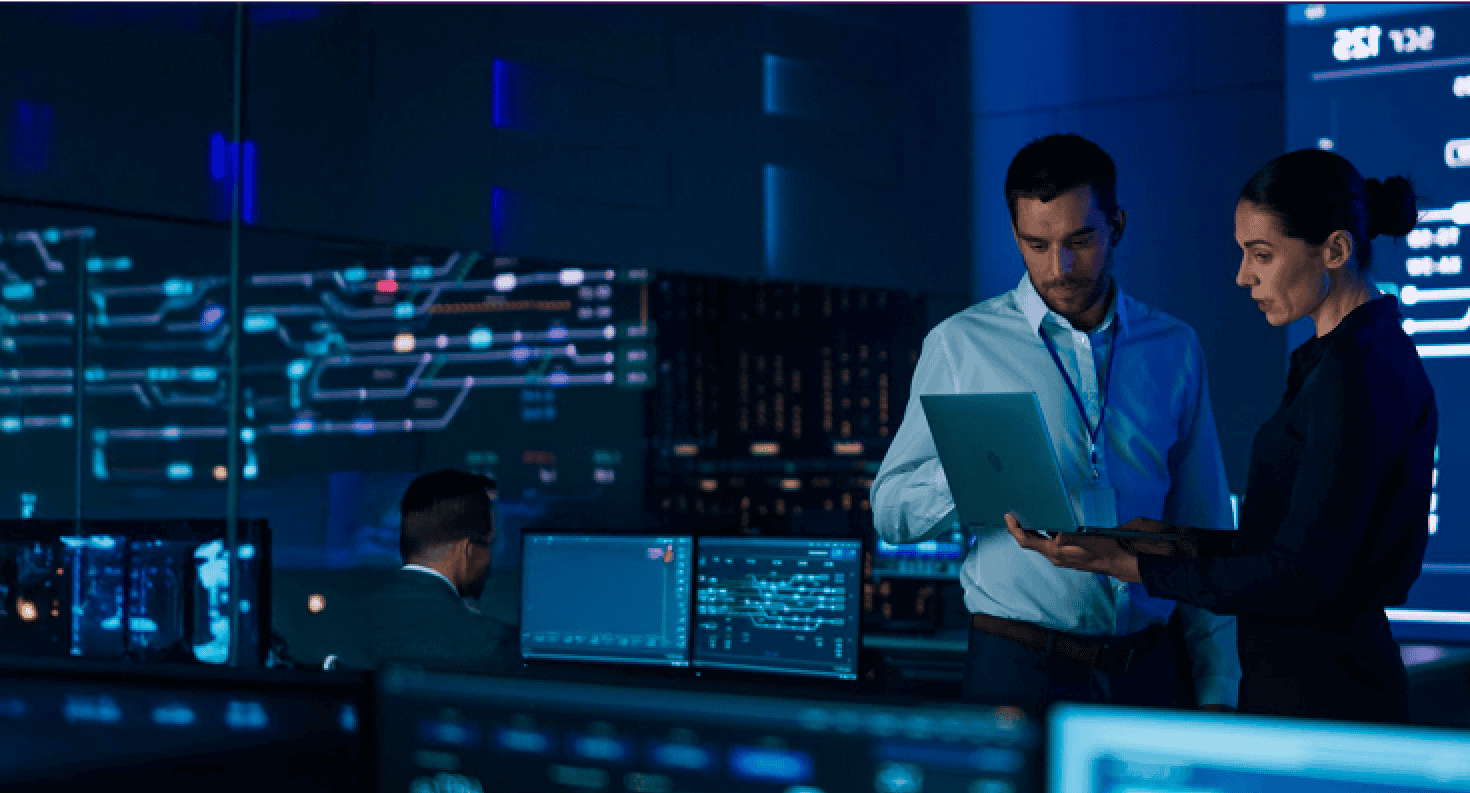
As your organization grows, so does the risk of introducing gaps in network visibility. Whether through mergers and acquisitions, network upgrades, a cloud migration, or address changes, can you be sure you’re maintaining 100% visibility?
Asset visibility is a critical component of effective cybersecurity and network management, yet it presents numerous challenges for organizations.
The dynamic nature of IT environments, with assets constantly being added, removed, or modified, makes it difficult to maintain an accurate and comprehensive inventory. This is compounded by the presence of shadow IT, where unauthorized devices and software are used without the knowledge of IT departments, further obscuring visibility.
FireMon Asset Manager provides real-time active, passive, and targeted network and device discovery to detect unknown, rogue, shadow clouds, network infrastructure, and endpoints in the enterprise.
FireMon Asset Manager provides a comprehensive inventory of all L2 and L3 devices in on-premises and cloud environments, with automatic device profiling and various discovery methods used to identify endpoints, routers, switches, and OT/IoT devices.
Asset Manager provides automatic device profiling and custom details to manage assets in various environments, enriched by external data integrations, and enhances capabilities with SOAR and vulnerability scanner integrations for faster response to potential threats.
Asset Manager offers the most robust, flexible API to share accurate asset knowledge with other sources, improving data fidelity, operational intelligence, and protecting your environment.
Asset Manager offers a complete view of the network, allowing for consistent enforcement of device policies and network security, and provides instant notification for policy violations, network vulnerability assessments, and leak detection between networks.
FireMon Asset Manager enables real-time detection of anomalies and violations, and offers preconfigured and customizable reports, custom notifications, and integrations to enhance capabilities, as well as network connectivity vulnerability and compliance testing.
Cybersecurity asset management involves identifying, monitoring, and protecting all assets within an organization’s IT environment. This includes hardware, virtual machines, cloud-based assets, and any other devices connected to the network. The goal is to ensure that all assets are identified, secure, compliant, and managed efficiently to reduce vulnerabilities and enhance overall cybersecurity posture.
FireMon Asset Manager can protect a wide range of assets, including but not limited to:
Asset management is crucial for cybersecurity because it provides visibility into all devices within an organization. This visibility helps identify and mitigate potential vulnerabilities, ensures compliance with security policies, and enhances incident response capabilities. Without effective asset management, it is challenging to protect critical assets, leading to increased risk of cyberattacks and data breaches.
Examples of cyber asset management include:
These practices help maintain a secure and compliant IT environment, reducing the risk of cyber threats.