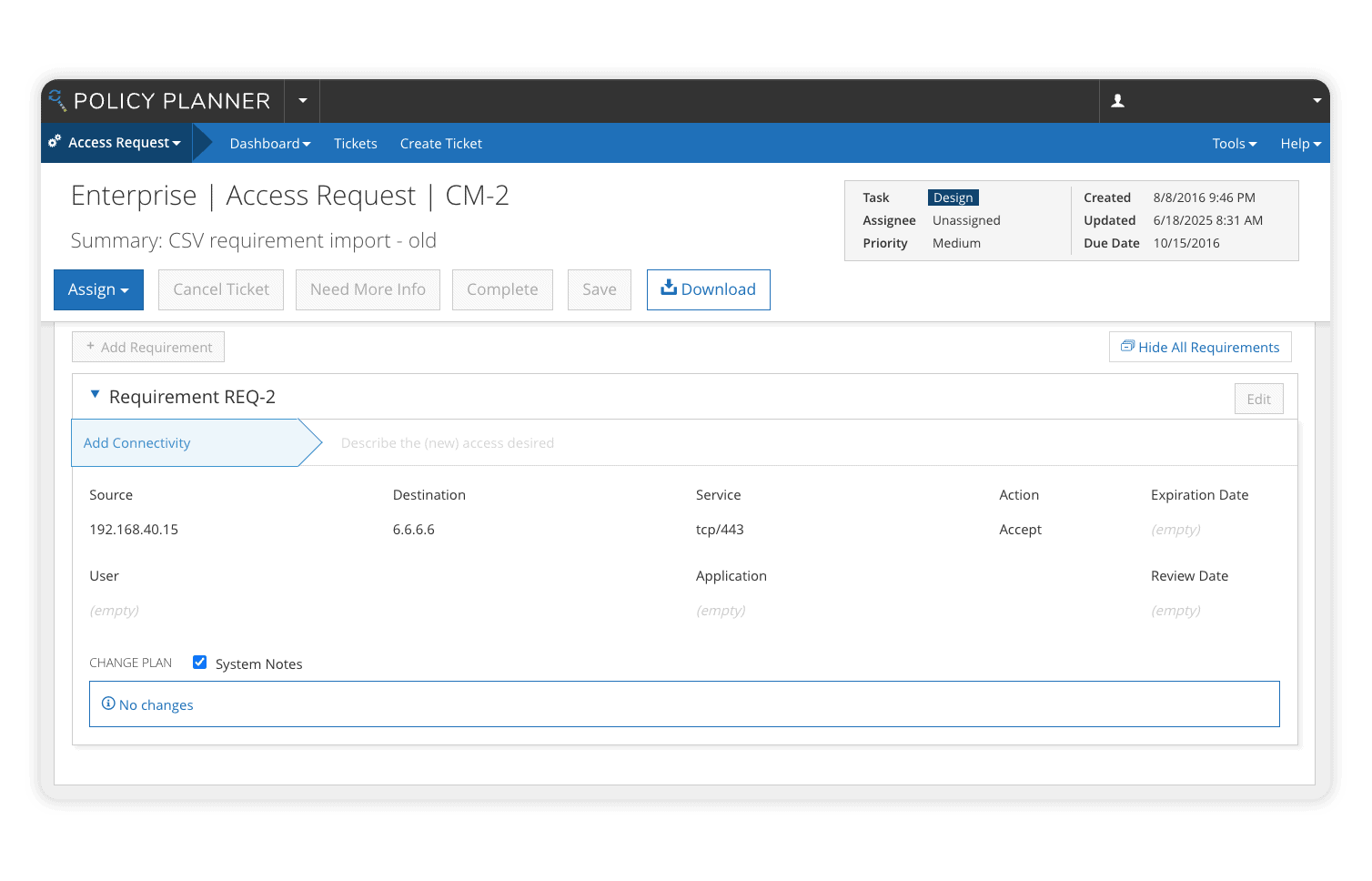
Change Firewall Policies, Not Your Security Posture
The overwhelming majority of firewall and cloud security breaches stem from misconfigurations, not the controls themselves. Beyond introducing opportunities for error and expanding the threat surface, manual change management processes for complex on-premises and cloud environments are resource-intensive and hinder business agility.